6
answers
1
watching
245
views
aminul2005Lv1
3 Feb 2022
A security auditor needs to review the manner in which an entertainment streaming device operates. The auditor is analyzing the output of a port scanning tool to determine the next steps in the security review. Given the following log output:
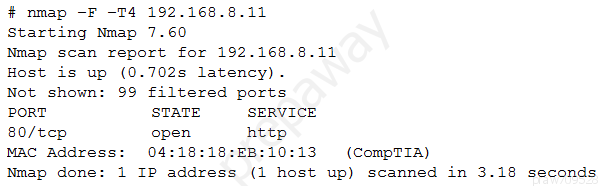
The best option for the auditor to use NEXT is:
- A. a SCAP assessment.
- B. reverse engineering.
- C. fuzzing.
- D. network interception.
A security auditor needs to review the manner in which an entertainment streaming device operates. The auditor is analyzing the output of a port scanning tool to determine the next steps in the security review. Given the following log output:
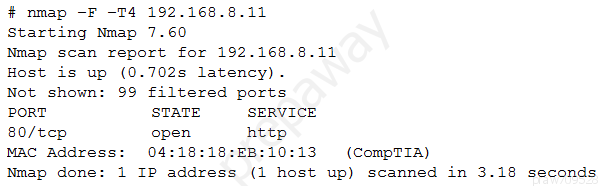
The best option for the auditor to use NEXT is:
- A. a SCAP assessment.
- B. reverse engineering.
- C. fuzzing.
- D. network interception.
Read by 2 people






